Lick ransomware removal instructions
Lick ransomware removal instructions
What is Lick?
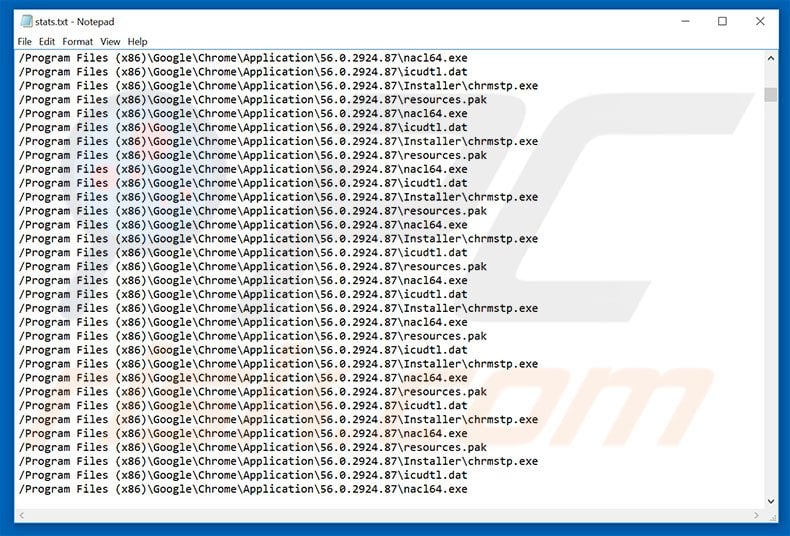
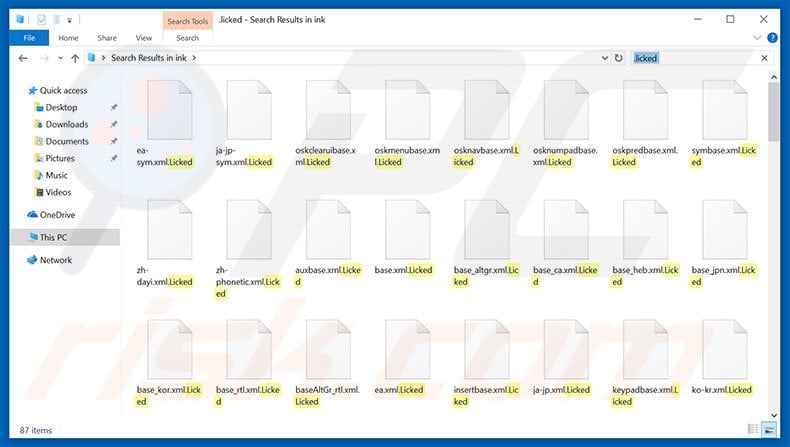
First discovered by malware researcher, Jakub Kroustek, Lick is a ransomware-type virus similar to Kirk. Once infiltrated, Lick encrypts various files and appends filenames with the ".Licked" extension. For example, "sample.jpg" is renamed to "sample.jpg.Licked". Lick then creates the following files: 1) "ERRORLOG.txt", containing a ransom-demand message; 2) "stats.txt", containing a list of encrypted files, and; 3) a pwd file, containing a decryption password, which unfortunately is also encrypted.
The message informs victims of the encryption and claims that files can only be restored using a decryption tool together with a password stored within the aforementioned pwd file. In fact, to restore the encrypted password and receive a decryption tool, victims must pay a ransom in the Monero cryptocurrency. The cost depends on how much time victims wait before paying: 0-2 days - 50 Monero; 3-7 days - 100 Monero; 8-14 days - 200 Monero, and; 15-30 days - 500 Monero. At time of writing, 1 Monero was equivalent to ~$23 and, hence, the cost essentially fluctuates between $1000 and $10000. If the ransom is not paid within one month, the decryption key (used to restore the password stored within the pwd file) is permanently deleted. Despite these demands, cyber criminals should never be trusted. Research shows that ransomware developers often ignore victims once payments are submitted - paying does not guarantee that your files will ever be decrypted and there is a high probability that you will be scammed. Therefore, never attempt to contact these people or pay any ransom. Unfortunately, there are no tools capable of restoring data encrypted by Lick and this problem can only be resolved by restoring files/system from a backup.
Screenshot of a message encouraging users to pay a ransom to decrypt their compromised data:

There are dozens of ransomware-type viruses virtually identical to Lick including ZinoCrypt, Crptxxx, and Revenge - these are just some examples from many. As with Lick, these malware infections also encrypt files and make ransom demands. The only major differences between ransomware-type viruses are size of ransom and type of encryption algorithm (symmetric or asymmetric) used. The distribution methods are also identical. Ransomware-type viruses are often distributed using spam emails (infectious attachments), peer-to-peer networks (eMule, torrents, etc.), third party software download sources (free file hosting websites, freeware download websites, etc.), fake software update tools, and trojans. Therefore, be cautious when opening files received from suspicious emails, and when downloading software from unofficial sources. Keep your installed applications up-to-date, but bear in mind that criminals often employ fake software updaters to proliferate malware. Therefore, never update your apps via third party tools. Using a legitimate anti-virus/anti-spyware suite is also very important. The key to computer safety is caution.
Screenshot of Lick text file:
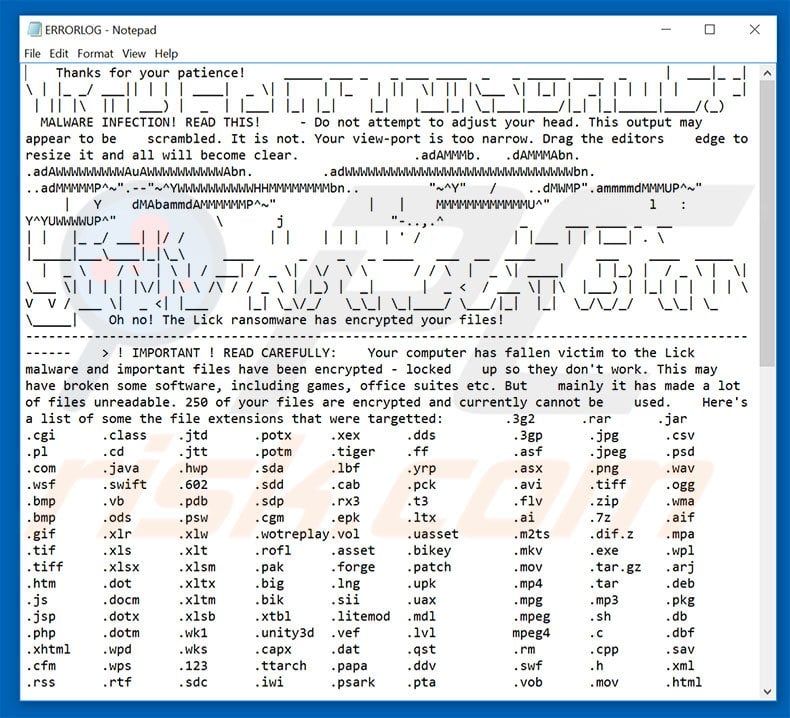
Text presented within Lick pop-up and text file:
Thanks for your patience!
MALWARE INFECTION! READ THIS!
- Do not attempt to adjust your head. This output may appear to be
scrambled. It is not. Your view-port is too narrow. Drag the editors
edge to resize it and all will become clear.
Oh no! The Lick ransomware has encrypted your files!
! IMPORTANT ! READ CAREFULLY:
Your computer has fallen victim to the Lick malware and important files have been encrypted - locked
up so they don't work. This may have broken some software, including games, office suites etc. But
mainly it has made a lot of files unreadable. 250 of your files are encrypted and currently cannot be
used.
Here's a list of some the file extensions that were targetted: -
There are an additional 436 file extensions that were targetted.
To get your files back, you need to pay. Now. Payments recieved more than 48 hours after the time of
infection will be charged double. Further time penalties are listed below. The time of infection has
been logged.
Any files with the extensions listed above will now have the extra extension '.Licked', these files
are encrypted using military grade encryption.
In the place you ran this program from, you should find a note (named RANSOM_NOTE.txt) similar to this one.
The note may also be named 'stats.txt' - this is a copy of this note, for your reference. There is also
a ERRORLOG.TXT file - this contains a list of all files that have been encrypted.
You will also find a file named 'pwd' - this is your encrypted password file. Although it was
generated by your computer, you have no way of ever decrypting it. This is due to both the way
it was generated and the way it was encrypted. Your files were encrypted using this password.
Oh no indeed.
To decrypt your .Licked files back to their original state, you need your pwd file to be decrypted.
And also the file decryption program. We will not supply either without the proper payment.
Decrypting your files is easy. Take a deep breath and follow the steps below.
1 ) Make the proper payment.
Payments are made in Monero. This is a crypto-currency, like bitcoin.
You can buy Monero, and send it, from the same places you can any other
crypto-currency. If you're still unsure, google 'bitcoin exchange'.
Sign up at one of these exchange sites and send the payment to the address below.
Make note of the payment / transaction ID, or make one up if you have the option.
Payment Address (Monero Wallet):
4AqSwfTexbNaHcn8giSJw3KPiWYHGBaCF9bdgPxvHbd5A8Q3Fc7n6FQCReEns8uEg8jUo4BeB79rwf4XSfQPVL1SKdVp2jz
Prices:
Days : Monero : Offer Expires
0-2 : 50 : 03/22/17 16:38:41
3-7 : 100 : 03/27/17 16:38:41
8-14 : 200 : 04/03/17 16:38:41
15-30 : 500 : 04/19/17 16:38:41
Note: In 31 days your password decryption key gets permanently deleted.
You then have no way to ever retrieve your files. So pay now.
2 ) Email us.
Send your pwd file as an email attachment to one of the email addresses below.
Include the payment ID from step 1.
Active email addresses:
kirk.payments@scryptmail.com
hanna.harrington@scryptmail.com
3 ) Decrypt your files.
You will recieve your decrypted password file and a file decryption program.
Download these both to the same place and run the decryption program. This reads
your decrypted password file and uses it to decrypt all of the affected files on
your computer.
> IMPORTANT !
The password is unique to this infection.
Using an old password or one from another machine will result in corrupted files.
Corrupted files cannot be fixed.
Don't fuck around.
4 ) Breathe.
Screenshot of file containing list of files encrypted by Lick:
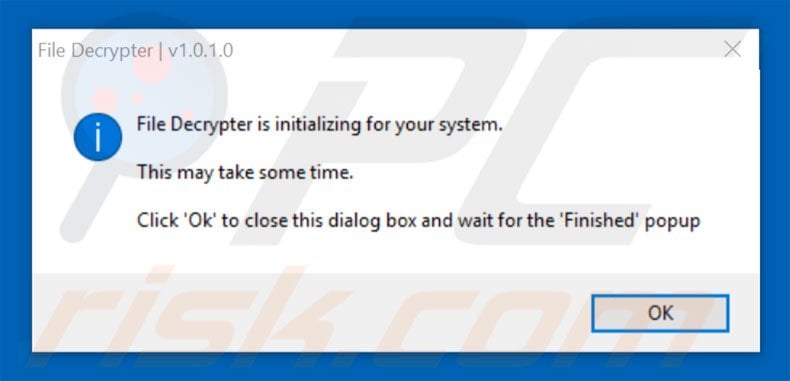
Screenshot of a pop-up appearing when Lick ransomware starts encrypting files:
Screenshot of files encrypted by Lick (".Licked" extension):
Lick ransomware removal:
Quick menu:Quick solution to remove .Licked virus
- What is Lick?
- STEP 1. Lick virus removal using safe mode with networking.
- STEP 2. Lick ransomware removal using System Restore.
Step 1
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
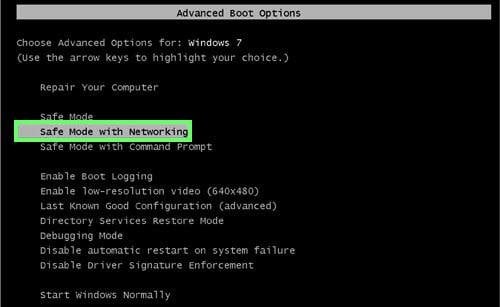
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup. Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings". Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
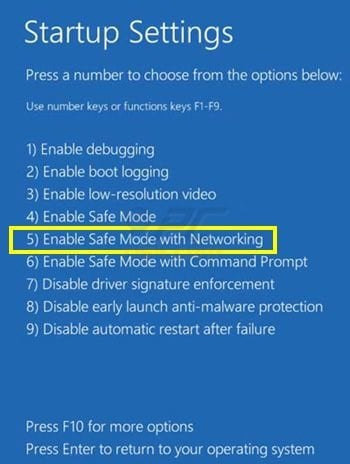
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options". In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
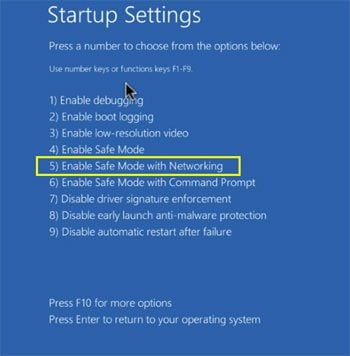
Video showing how to start Windows 10 in "Safe Mode with Networking":
Step 2
Log in to the account infected with the Lick virus. Start your Internet browser and download a legitimate anti-spyware program. Update the anti-spyware software and start a full system scan. Remove all entries detected.
If you need assistance removing lick , give us a call 24/7:
1-866-208-0865
1-866-208-0865
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. SpyHunter’s free scanner is for malware detection. To remove the detected infections you will need to purchase a full version of this product. More information on SpyHunter. If you wish to uninstall SpyHunter follow these instructions. All the products we recommend were carefully tested and approved by our technicians as being one of the most effective solutions for removing this threat.
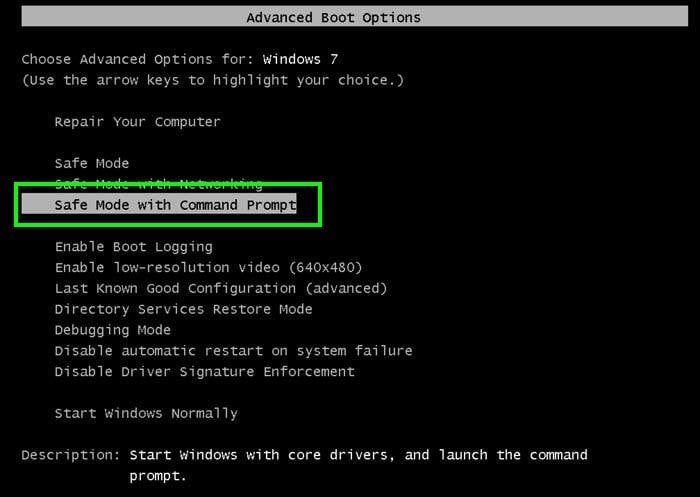
If you cannot start your computer in Safe Mode with Networking, try performing a System Restore.
Video showing how to remove ransomware virus using "Safe Mode with Command Prompt" and "System Restore":
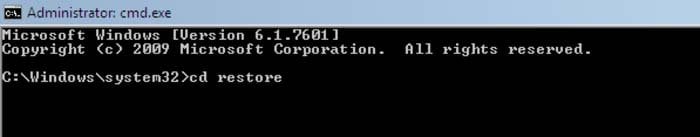
1. During your computer start process, press the F8 key on your keyboard multiple times until the Windows Advanced Options menu appears, and then select Safe Mode with Command Prompt from the list and press ENTER.
2. When Command Prompt mode loads, enter the following line: cd restore and press ENTER.
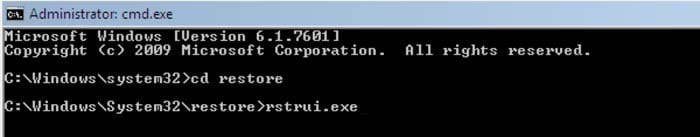
3. Next, type this line: rstrui.exe and press ENTER.
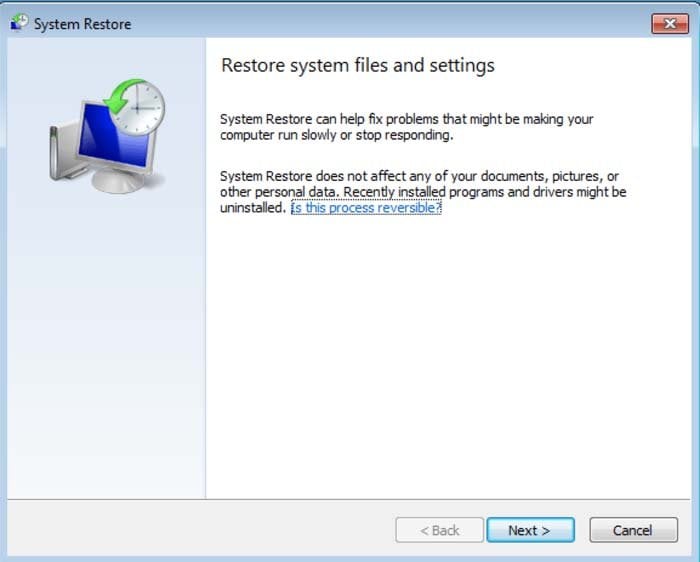
4. In the opened window, click "Next".
5. Select one of the available Restore Points and click "Next" (this will restore your computer system to an earlier time and date, prior to the Lick ransomware virus infiltrating your PC).
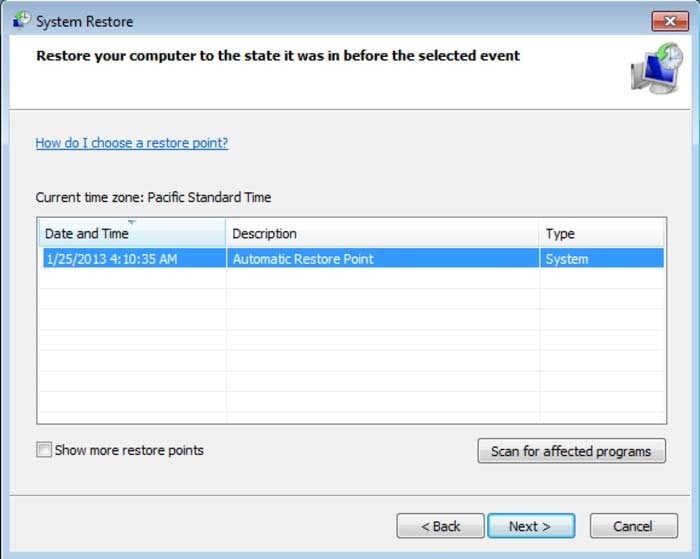
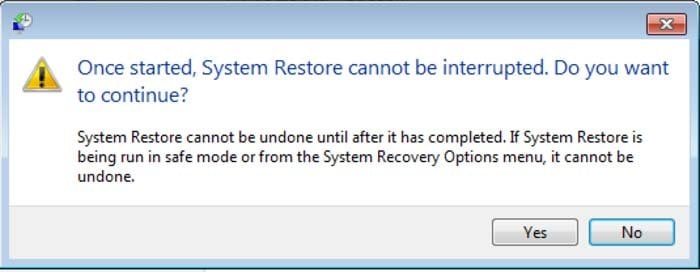
6. In the opened window, click "Yes".
7. After restoring your computer to a previous date, download and scan your PC with recommended malware removal software to eliminate any remaining Lick ransomware files.
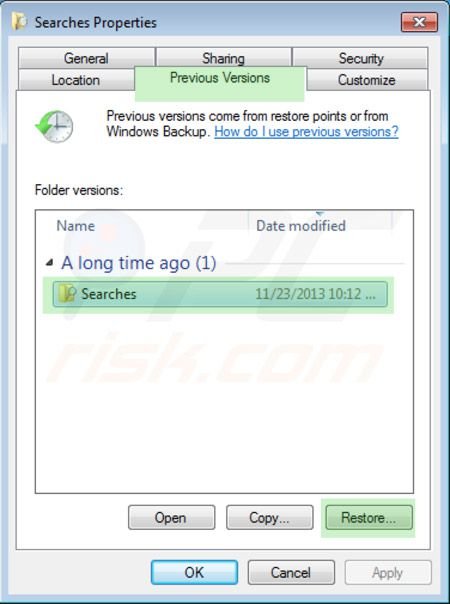
To restore individual files encrypted by this ransomware, try using Windows Previous Versions feature. This method is only effective if the System Restore function was enabled on an infected operating system. Note that some variants of Lick are known to remove Shadow Volume Copies of the files, so this method may not work on all computers.
To restore a file, right-click over it, go into Properties, and select the Previous Versions tab. If the relevant file has a Restore Point, select it and click the "Restore" button.
If you cannot start your computer in Safe Mode with Networking (or with Command Prompt), boot your computer using a rescue disk. Some variants of ransomware disable Safe Mode making its removal complicated. For this step, you require access to another computer.
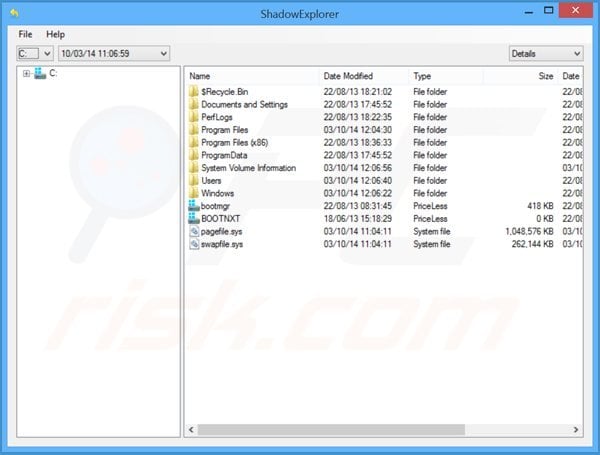
To regain control of the files encrypted by Lick, you can also try using a program called Shadow Explorer. More information on how to use this program is available here.
To protect your computer from file encryption ransomware such as this, use reputable antivirus and anti-spyware programs. As an extra protection method, you can use programs called HitmanPro.Alert and EasySync CryptoMonitor, which artificially implant group policy objects into the registry to block rogue programs such as Lick ransomware.
HitmanPro.Alert CryptoGuard - detects encryption of files and neutralises any attempts without need for user-intervention:

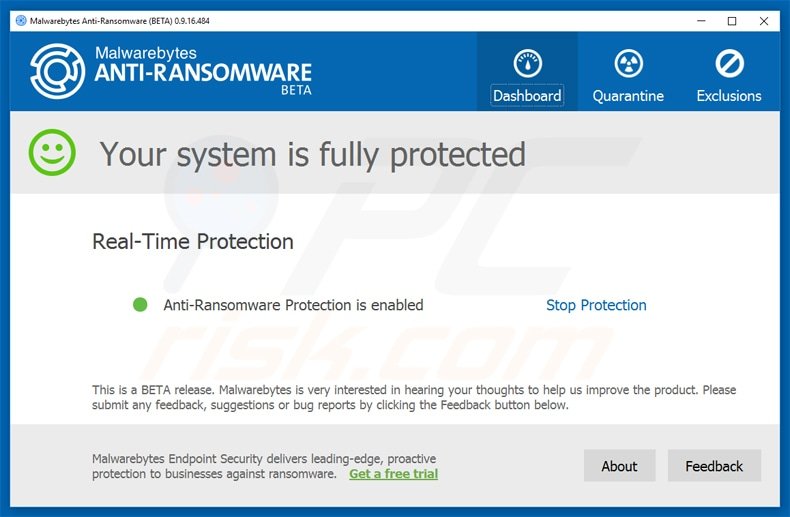
Malwarebytes Anti-Ransomware Beta uses advanced proactive technology that monitors ransomware activity and terminates it immediately - before reaching users' files:
- The best way to avoid damage from ransomware infections is to maintain regular up-to-date backups. More information on online backup solutions and data recovery software Here.
Comments
Post a Comment