Remove Unlock26 ransomware
Unlock26 ransomware removal instructions
What is Unlock26?
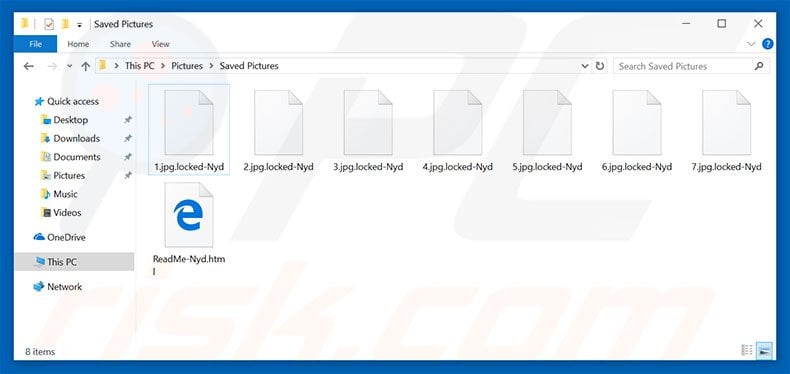
Unlock26 is a ransomware-type virus discovered by MalwareHunterTeam. Once infiltrated, Unlock26 encrypts files and appends filenames with the ".locked-Nyd" extension. For example, "sample.jpg" is renamed to "sample.jpg.locked-Nyd". Unlock26 then creates an HTML file ("ReadMe-Nyd.html"), placing it in each folder containing encrypted files.
The "ReadMe-Nyd.HTML" file contains a message informing victims of the encryption and encourages them to visit one of the links provided for further information. Unlock26's website claims that, to restore files, victims must pay a ransom of 0.06 (6.e-002) Bitcoins (approximately, $70). It is currently unknown whether Unlock26uses symmetric or asymmetric cryptography. In any case, decryption without a unique key is impossible. Cyber criminals store this key on a remote server and users are encouraged to purchase it, otherwise their files will never be decrypted. Be aware, however, that cyber criminals should never be trusted. Research shows that criminals often ignore victims, once payments are submitted. There is no guarantee that paying will give any positive result. You will probably be scammed. Therefore, never attempt to contact these people or pay any ransom. Unfortunately, there are no tools capable of restoring files encrypted by Unlock26 - you can only restore your files/system from a backup.
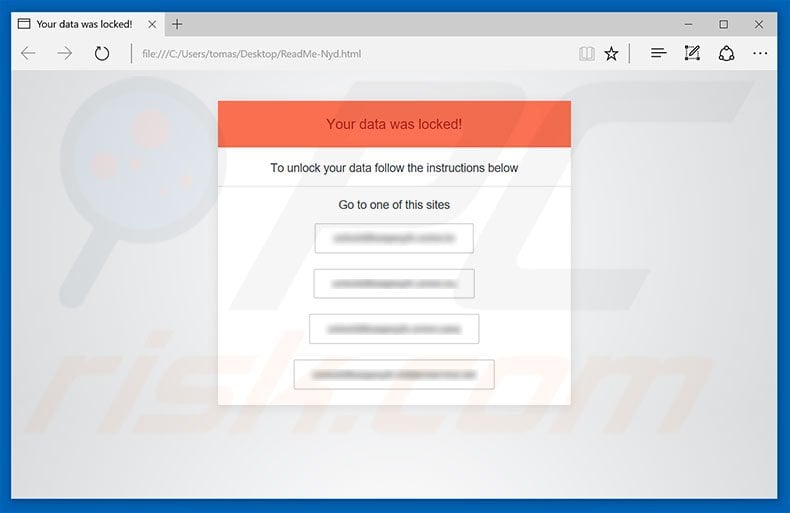
Screenshot of a message encouraging users to visit rogue websites to decrypt their compromised data:
Unlock26 shares many similarities with dozens of other ransomware-type viruses. As with Unlock26, malware such as Purge, Hermes, FadeSoft, and many others, also encrypt files and make ransom demands. In fact, there are just two major differences between ransomware-type viruses: 1) type of encryption algorithm [symmetric/asymmetric] used, and; 2) cost of decryption. The distribution methods are also identical. Cyber criminals proliferate ransomware by employing spam emails (infectious attachments), peer-to-peer (P2P) networks (torrents, eMule, etc.), third party download sources (freeware download websites, free file hosting websites, etc.), fake software update tools, and trojans. Therefore, be cautious when opening files received from suspicious emails, and when downloading software/files from unofficial sources. Furthermore, keep your installed applications up-to-date and use a legitimate anti-virus/anti-spyware suite. Bear in mind, however, that criminals often employ fake software updaters to spread malware. Therefore, never use any third party update tools. Reckless behavior and poor knowledge are often the reasons for computer infections. The key to computer safety is caution.
Screenshot of Unlock26 website:
First page (website checks if you are human):
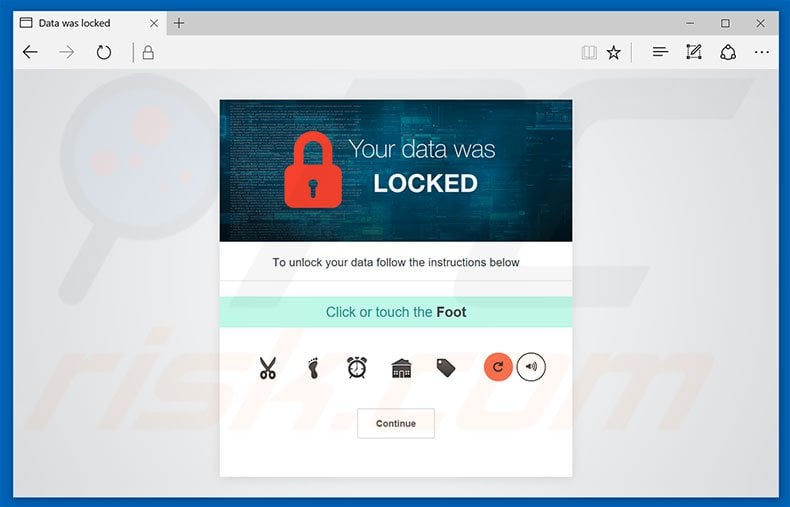
Second page:
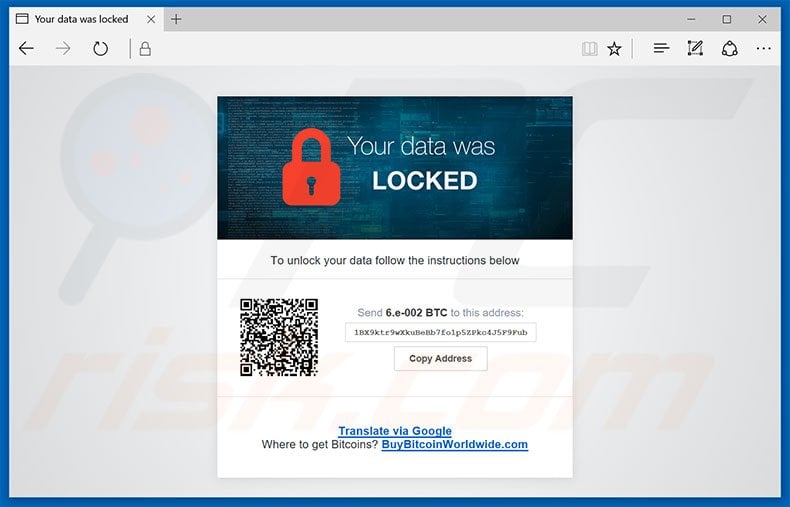
Text presented within this page:
To unlock your data follow the instructions below
Send 6.e-002 BTC to this address:
1BX9ktr9wXkuBeBb7fo1p5ZPkc4J5F9Fub
Screenshot of files encrypted by Unlock26 (".locked-Nyd" extension):
Unlock26 ransomware removal:
Quick menu:Quick solution to remove .locked-Nyd virus
- What is Unlock26?
- STEP 1. Unlock26 virus removal using safe mode with networking.
- STEP 2. Unlock26 ransomware removal using System Restore.
Step 1
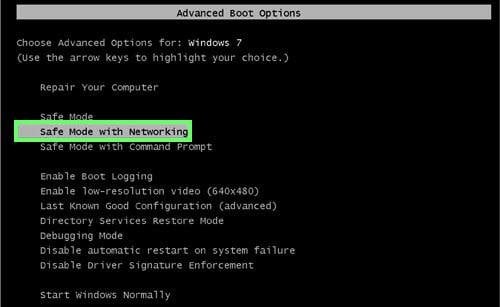
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
Video showing how to start Windows 7 in "Safe Mode with Networking":
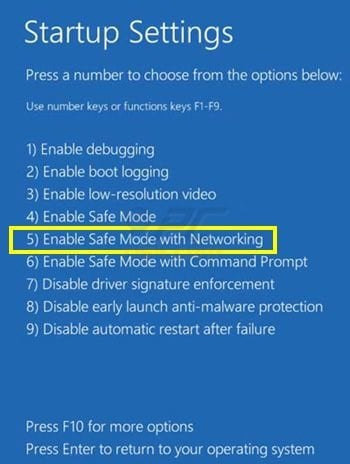
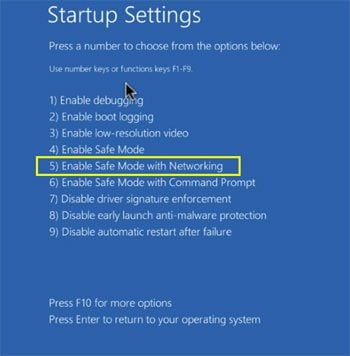
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup. Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings". Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options". In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
Step 2
Log in to the account infected with the Unlock26 virus. Start your Internet browser and download a legitimate anti-spyware program. Update the anti-spyware software and start a full system scan. Remove all entries detected.
If you need assistance removing unlock26 , give us a call 24/7:
1-866-208-0865
1-866-208-0865
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. SpyHunter’s free scanner is for malware detection. To remove the detected infections you will need to purchase a full version of this product. More information on SpyHunter. If you wish to uninstall SpyHunter follow these instructions. All the products we recommend were carefully tested and approved by our technicians as being one of the most effective solutions for removing this threat.
If you cannot start your computer in Safe Mode with Networking, try performing a System Restore.
Video showing how to remove ransomware virus using "Safe Mode with Command Prompt" and "System Restore":
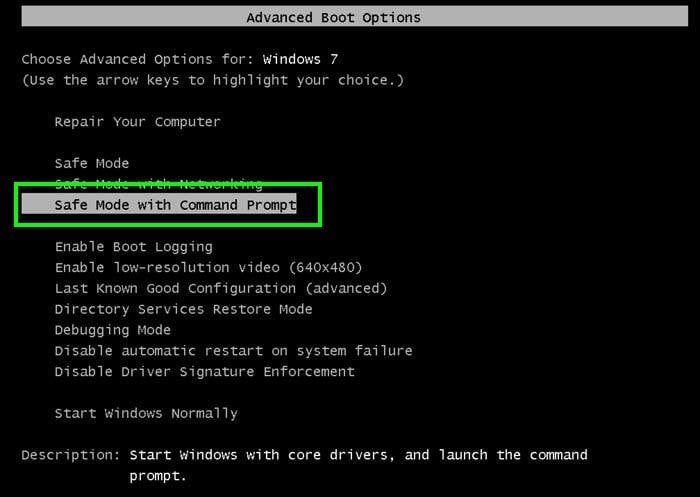
1. During your computer start process, press the F8 key on your keyboard multiple times until the Windows Advanced Options menu appears, and then select Safe Mode with Command Prompt from the list and press ENTER.
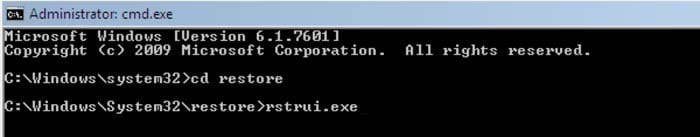
2. When Command Prompt mode loads, enter the following line: cd restore and press ENTER.
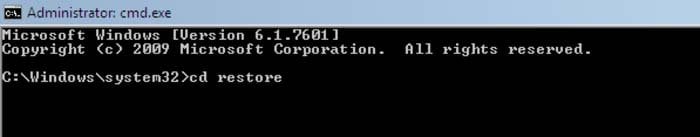
3. Next, type this line: rstrui.exe and press ENTER.
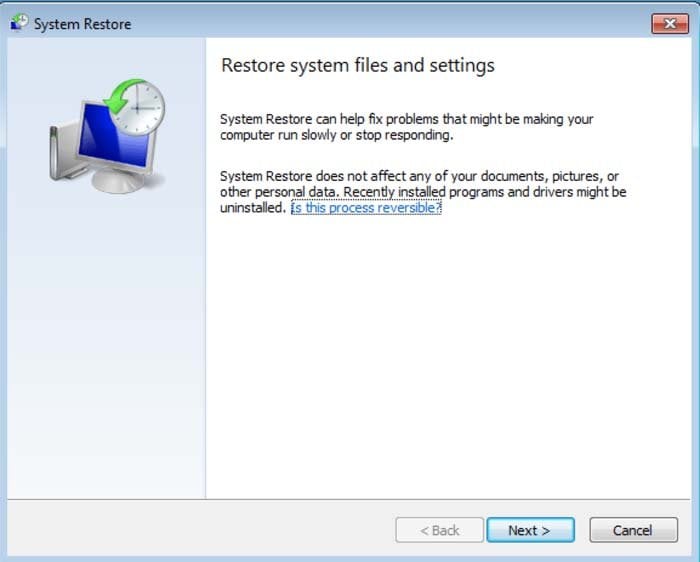
4. In the opened window, click "Next".
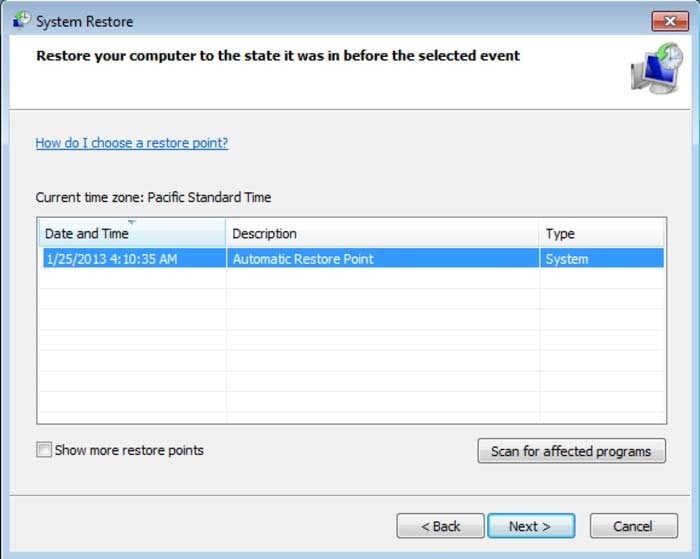
5. Select one of the available Restore Points and click "Next" (this will restore your computer system to an earlier time and date, prior to the Unlock26 ransomware virus infiltrating your PC).
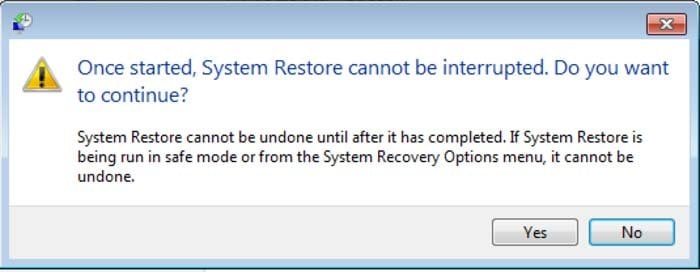
6. In the opened window, click "Yes".
7. After restoring your computer to a previous date, download and scan your PC with recommended malware removal software to eliminate any remaining Unlock26 ransomware files.
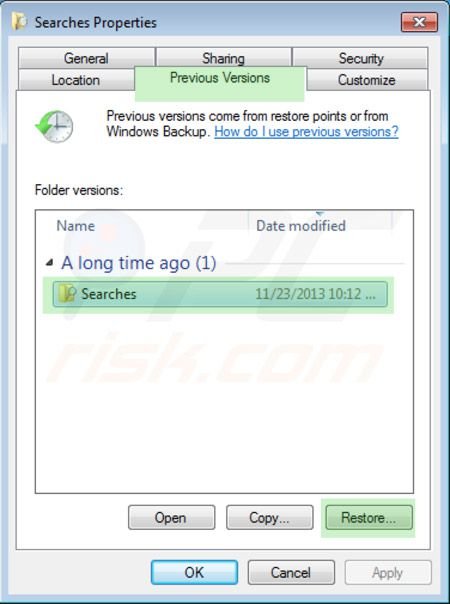
To restore individual files encrypted by this ransomware, try using Windows Previous Versions feature. This method is only effective if the System Restore function was enabled on an infected operating system. Note that some variants of Unlock26 are known to remove Shadow Volume Copies of the files, so this method may not work on all computers.
To restore a file, right-click over it, go into Properties, and select the Previous Versions tab. If the relevant file has a Restore Point, select it and click the "Restore" button.
If you cannot start your computer in Safe Mode with Networking (or with Command Prompt), boot your computer using a rescue disk. Some variants of ransomware disable Safe Mode making its removal complicated. For this step, you require access to another computer.
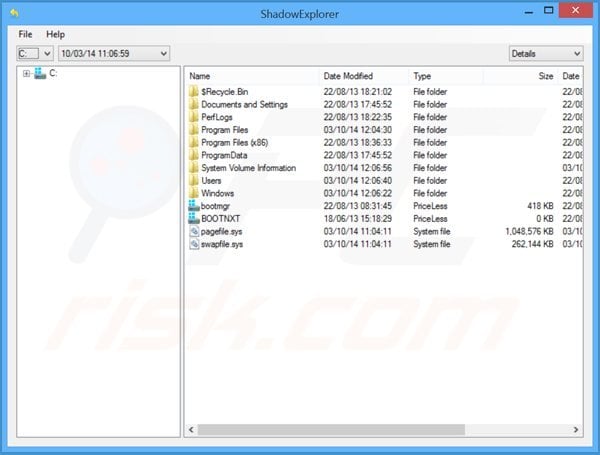
To regain control of the files encrypted by Unlock26, you can also try using a program called Shadow Explorer. More information on how to use this program is available here.
To protect your computer from file encryption ransomware such as this, use reputable antivirus and anti-spyware programs. As an extra protection method, you can use programs called HitmanPro.Alert and EasySync CryptoMonitor, which artificially implant group policy objects into the registry to block rogue programs such as Unlock26 ransomware.
HitmanPro.Alert CryptoGuard - detects encryption of files and neutralises any attempts without need for user-intervention:

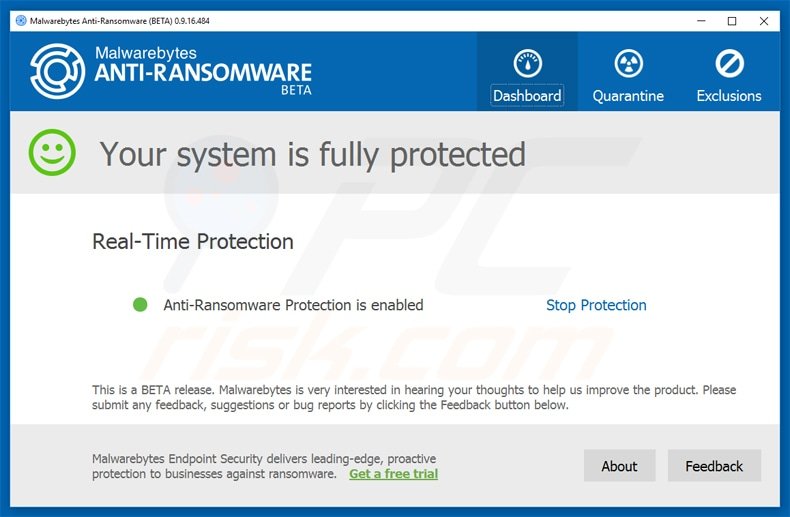
Malwarebytes Anti-Ransomware Beta uses advanced proactive technology that monitors ransomware activity and terminates it immediately - before reaching users' files:
- The best way to avoid damage from ransomware infections is to maintain regular up-to-date backups. More information on online backup solutions and data recovery software Here.
Comments
Post a Comment